How To Install Ssl Certificate Digitalocean
Introduction
This tutorial will show you how to learn and install an SSL document from a trusted, commercial Document Authorization (CA). SSL certificates permit web servers to encrypt their traffic, and also offering a mechanism to validate server identities to their visitors. The main do good of using a purchased SSL certificate from a trusted CA, over cocky-signed certificates, is that your site's visitors volition not be presented with a scary warning about non being able to verify your site's identity.
This tutorial covers how to acquire an SSL certificate from the following trusted document authorities:
- GoDaddy
- RapidSSL (via Namecheap)
You may likewise use any other CA of your choice.
Subsequently you have acquired your SSL certificate, we will testify y'all how to install it on Nginx and Apache HTTP web servers.
Prerequisites
There are several prerequisites that you lot should ensure before attempting to obtain an SSL certificate from a commercial CA. This department will cover what you volition need in social club to be issued an SSL document from nearly CAs.
Money
SSL certificates that are issued from commercial CAs accept to be purchased. The all-time gratis culling are certificates issued from Let'south Encrypt. Allow's Encrypt is a new certificate authority that issues free SSL/TLS certificates that are trusted in almost web browsers.
Registered Domain Proper noun
Before acquiring an SSL document, you must own or command the registered domain name that you lot wish to utilize the certificate with. If you do non already have a registered domain name, you may register ane with one of the many domain name registrars out in that location (east.g. Namecheap, GoDaddy, etc.).
Domain Validation Rights
For the basic domain validation process, you must accept access to one of the email addresses on your domain's WHOIS tape or to an "admin type" email accost at the domain itself. Certificate authorities that issue SSL certificates will typically validate domain control by sending a validation email to 1 of the addresses on the domain's WHOIS record, or to a generic admin email address at the domain itself. Some CAs provide alternative domain validation methods, such as DNS- or HTTP-based validation, which are outside the scope of this guide.
If y'all wish to be issued an Organization Validation (OV) or Extended Validation (EV) SSL certificate, you will also exist required to provide the CA with paperwork to institute the legal identity of the website's owner, amid other things.
Web Server
In addition to the previously mentioned points, y'all volition need a web server to install the SSL certificate on. This is the server that is reachable at the domain proper name for which the SSL certificate will be issued for. Typically, this will be an Apache HTTP, Nginx, HAProxy, or Varnish server. If y'all demand help setting up a web server that is attainable via your registered domain name, follow these steps:
- Ready a spider web server of your selection. For instance, a LEMP (Nginx) or LAMP (Apache) server–exist certain to configure the spider web server software to use the name of your registered domain
- Configure your domain to utilize the advisable nameservers. If your web server is hosted on DigitalOcean, this guide can assistance yous go prepare up: How To Point to DigitalOcean'south Nameservers from Mutual Domain Registrars
- Add DNS records for your web server to your nameservers. If you are using DigitalOcean's nameservers, follow this guide to learn how to add together the appropriate records: How To Ready a Host Name with DigitalOcean
Choose Your Certificate Authority
If you are non sure of which Certificate Authority you are going to utilise, there are a few important factors to consider. At an overview level, the most important thing is that the CA yous choose provides the features you desire at a price that you are comfortable with. This section will focus more on the features that most SSL certificate buyers should be aware of, rather than prices.
Root Document Program Memberships
The nigh crucial point is that the CA that yous choose is a fellow member of the root certificate programs of the most commonly used operating systems and web browsers, i.e. it is a "trusted" CA, and its root certificate is trusted by common browsers and other software. If your website's SSL certificate is signed past a trusted" CA, its identity is considered to be valid past software that trusts the CA–this is in contrast to cocky-signed SSL certificates, which also provide encryption capabilities but are accompanied past identity validation warnings that are off-putting to virtually website visitors.
Nigh commercial CAs that you will encounter will exist members of the common root CA programs, and will say they are compatible with 99% of browsers, merely information technology does not injure to check before making your certificate buy. For example, Apple provides its list of trusted SSL root certificates for iOS8 here.
Document Types
Ensure that you lot choose a CA that offers the certificate type that you require. Many CAs offering variations of these certificate types under a variety of, frequently confusing, names and pricing structures. Here is a brusk clarification of each blazon:
- Single Domain: Used for a single domain, due east.thousand.
example.com. Notation that boosted subdomains, such asworld wide web.example.com, are non included - Wildcard: Used for a domain and any of its subdomains. For case, a wildcard document for
*.instance.comtin can also be used forwww.example.comandstore.example.com - Multiple Domain: Known as a SAN or UC certificate, these can be used with multiple domains and subdomains that are added to the Subject Culling Proper name field. For example, a single multi-domain certificate could be used with
instance.com,www.instance.com, andcase.cyberspace
In addition to the aforementioned certificate types, there are unlike levels of validations that CAs offer. We volition embrace them hither:
- Domain Validation (DV): DV certificates are issued after the CA validates that the requestor owns or controls the domain in question
- System Validation (OV): OV certificates tin exist issued only later on the issuing CA validates the legal identity of the requestor
- Extended Validation (EV): EV certificates tin can exist issued only after the issuing CA validates the legal identity, among other things, of the requestor, co-ordinate to a strict set up of guidelines. The purpose of this type of document is to provide additional assurance of the legitimacy of your organization'due south identity to your site's visitors. EV certificates can be single or multiple domain, just not wildcard
This guide will show yous how to obtain a single domain or wildcard SSL document from GoDaddy and RapidSSL, but obtaining the other types of certificates is very similar.
Additional Features
Many CAs offering a big diverseness of "bonus" features to differentiate themselves from the rest of the SSL certificate-issuing vendors. Some of these features tin can end up saving you money, then it is of import that you lot weigh your needs against the offerings carefully earlier making a purchase. Instance of features to expect out for include free certificate reissues or a unmarried domain-priced document that works for www. and the domain basename, e.yard. world wide web.instance.com with a SAN of example.com
Generate a CSR and Private Key
After you have all of your prerequisites sorted out, and you know the type of certificate yous want to become, information technology'due south time to generate a certificate signing asking (CSR) and private key.
If yous are planning on using Apache HTTP or Nginx as your spider web server, apply openssl to generate your individual primal and CSR on your web server. In this tutorial, we will just keep all of the relevant files in our home directory but feel free to shop them in any secure location on your server:
cd ~ To generate a individual central, called example.com.key, and a CSR, chosen example.com.csr, run this control (supersede the case.com with the name of your domain):
openssl req -newkey rsa:2048 -nodes -keyout example.com.key -out case.com.csr At this point, you will be prompted for several lines of information that volition be included in your certificate request. The most important role is the Mutual Proper name field which should match the name that you lot want to apply your document with–for example, example.com, www.example.com, or (for a wildcard certificate request) *.example.com. If you are planning on getting an OV or EV document, ensure that all of the other fields accurately reflect your arrangement or business organisation details.
For example:
State Proper noun (2 letter lawmaking) [AU]:Us Country or Province Proper name (full name) [Some-State]:New York Locality Proper noun (eg, urban center) []:New York Organization Name (eg, company) [Internet Widgits Pty Ltd]:My Company Organizational Unit Proper noun (eg, section) []: Common Proper name (e.chiliad. server FQDN or YOUR name) []:example.com E-mail Accost []:sammy@example.com This will generate a .primal and .csr file. The .key file is your private key, and should be kept secure. The .csr file is what y'all volition send to the CA to request your SSL document.
You will demand to re-create and paste your CSR when submitting your certificate request to your CA. To impress the contents of your CSR, use this command (replace the filename with your ain):
cat case.com.csr Now we are fix to buy a certificate from a CA. We will show two examples, GoDaddy and RapidSSL via Namecheap, but feel gratis to get a certificate from any other vendor.
Example CA 1: RapidSSL via Namecheap
Namecheap provides a style to purchase SSL certificates from a diversity of CAs. We will walk through the process of acquiring a single domain document from RapidSSL, but you tin deviate if you want a different blazon of certificate.
Annotation: If you asking a single domain document from RapidSSL for the www subdomain of your domain (e.grand. www.case.com), they will upshot the document with a SAN of your base domain. For example, if your certificate request is for world wide web.example.com, the resulting certificate volition piece of work for both www.example.com and example.com.
Select and Purchase Certificate
Go to Namecheap's SSL certificate folio: https://www.namecheap.com/security/ssl-certificates.aspx.
Hither you can start selecting your validation level, certificate type ("Domains Secured"), or CA ("Make").
For our example, we will click on the Compare Products button in the "Domain Validation" box. Then we will find "RapidSSL", and click the Add together to Cart push button.
At this point, y'all must register or log in to Namecheap. Then finish the payment process.
Request Certificate
After paying for the document of your selection, go to the Manage SSL Certificates link, nether the "Hi Username" section.
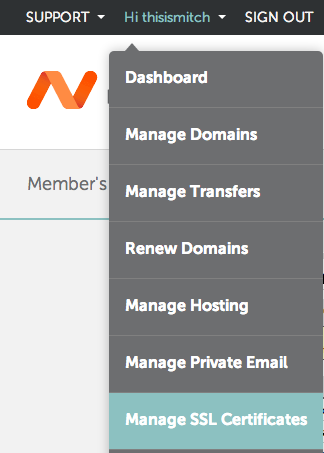
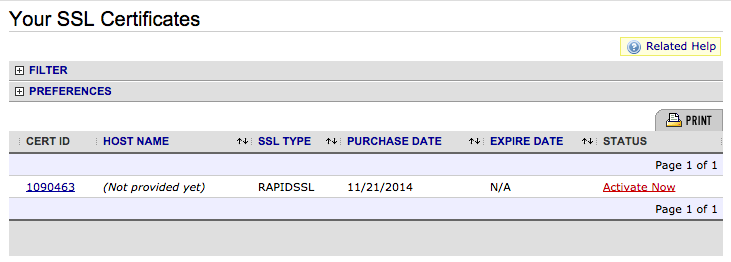
Hither, you volition see a list of all of the SSL certificates that yous accept purchased through Namecheap. Click on the Activate Now link for the document that y'all desire to use.
At present select the software of your web server. This will determine the format of the certificate that Namecheap will evangelize to you. Ordinarily selected options are "Apache + MOD SSL", "nginx", or "Tomcat".
Paste your CSR into the box then click the Next button.
You should at present be at the "Select Approver" step in the process, which volition ship a validation asking e-mail to an address in your domain'due south WHOIS record or to an administrator type address of the domain that you are getting a document for. Select the accost that y'all want to send the validation email to.
Provide the "Administrative Contact Information". Click the Submit order button.
Validate Domain
At this point, an electronic mail volition be sent to the "approver" accost. Open up the email and approve the document request.
Download Certificates
After approving the certificate, the certificate volition exist emailed to the Technical Contact. The document issued for your domain and the CA'due south intermediate certificate will exist at the bottom of the email.
Copy and save them to your server in the same location that you generated your private key and CSR. Name the certificate with the domain proper name and a .crt extension, east.g. example.com.crt, and name the intermediate certificate intermediate.crt.
The certificate is at present ready to be installed on your spider web server.
Example CA ii: GoDaddy
GoDaddy is a pop CA, and has all of the basic certificate types. Nosotros volition walk through the process of acquiring a single domain certificate, just you can deviate if y'all want a unlike type of document.
Select and Purchase Document
Go to GoDaddy'due south SSL certificate page: https://world wide web.godaddy.com/ssl/ssl-certificates.aspx.
Scroll down and click on the Get Started push.
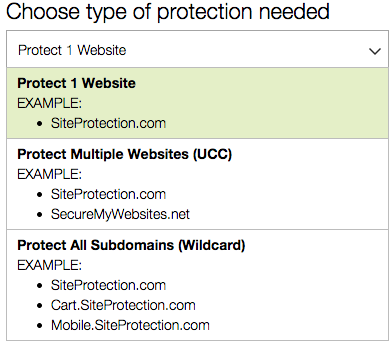
Select the type of SSL document that you desire from the drib downwards menu: unmarried domain, multidomain (UCC), or wildcard.
Then select your plan type: domain, organization, or extended validation.
Then select the term (duration of validity).
Then click the Add to Cart button.
Review your current order, then click the Go on to Checkout button.
Complete the registration and payment procedure.
Request Certificate
After you complete your order, click the SSL Certificates* push (or click on My Business relationship > Manage SSL Certificates in the top-right corner).
Find the SSL certificate that you just purchased and click the Set Upwardly push. If you have non used GoDaddy for SSL certificates earlier, you will be prompted to gear up the "SSL Certificates" product, and acquaintance your recent certificate order with the production (Click the green Gear up Up button and await a few minutes before refreshing your browser).
After the "SSL Certificates" Product is added to your GoDaddy business relationship, you should run across your "New Certificate" and a "Launch" button. Click on the Launch button adjacent to your new certificate.
Provide your CSR past pasting information technology into the box. The SHA-2 algorithm will be used by default.
Tick the I agree checkbox, and click the Request Document push button.
Validate Domain
Now y'all will have to verify that you lot have control of the domain, and provide GoDaddy with a few documents. GoDaddy will transport a domain ownership verification electronic mail to the address that is on your domain's WHOIS record. Follow the directions in the emails that you are sent to you, and authorize the issuance of the certificate.
Download Certificate
After verifying to GoDaddy that you control the domain, cheque your email (the one that you registered with GoDaddy with) for a message that says that your SSL certificate has been issued. Open it, and follow the download certificate link (or click the Launch push next to your SSL certificate in the GoDaddy control panel).
Now click the Download button.
Select the server software that you lot are using from the Server type dropdown menu–if yous are using Apache HTTP or Nginx, select "Apache"–and then click the Download Cipher File button.
Extract the ZIP archive. It should incorporate two .crt files; your SSL certificate (which should have a random proper name) and the GoDaddy intermediate document bundle (gd_bundle-g2-one.crt). Copy both two your web server. Rename the certificate to the domain name with a .crt extension, due east.k. example.com.crt, and rename the intermediate certificate parcel as intermediate.crt.
The certificate is at present set to be installed on your web server.
Install Certificate On Web Server
Later acquiring your certificate from the CA of your choice, y'all must install it on your spider web server. This involves adding a few SSL-related lines to your web server software configuration.
We will encompass basic Nginx and Apache HTTP configurations on Ubuntu 14.04 in this section.
We will assume the following things:
- The private primal, SSL certificate, and, if applicable, the CA's intermediate certificates are located in a habitation directory at
/home/sammy - The private key is called
example.com.primal - The SSL document is chosen
example.com.crt - The CA intermediate certificate(south) are in a file called
intermediate.crt - If you have a firewall enabled, be certain that it allows port 443 (HTTPS)
Note: In a real environment, these files should be stored somewhere that just the user that runs the web server master process (usually root) can access. The private primal should be kept secure.
Nginx
If you desire to apply your document with Nginx on Ubuntu xiv.04, follow this department.
With Nginx, if your CA included an intermediate certificate, y'all must create a single "chained" certificate file that contains your certificate and the CA's intermediate certificates.
Modify to the directory that contains your individual key, certificate, and the CA intermediate certificates (in the intermediate.crt file). Nosotros will assume that they are in your habitation directory for the example:
cd ~ Assuming your document file is called example.com.crt, use this command to create a combined file called instance.com.chained.crt (supplant the highlighted part with your own domain):
cat example.com.crt intermediate.crt > example.com.chained.crt Now go to your Nginx server block configuration directory. Assuming that is located at /etc/nginx/sites-enabled, use this control to change to it:
cd /etc/nginx/sites-enabled Assuming want to add SSL to your default server cake file, open up the file for editing:
sudo vi default Find and modify the heed directive, and modify information technology so information technology looks like this:
listen 443 ssl; Then find the server_name directive, and brand certain that its value matches the common name of your document. Besides, add the ssl_certificate and ssl_certificate_key directives to specify the paths of your certificate and private primal files (replace the highlighted part with the actual path of your files):
server_name example.com; ssl_certificate /dwelling house/sammy/example.com.chained.crt; ssl_certificate_key /home/sammy/case.com.primal; To permit only the near secure SSL protocols and ciphers, add the following lines to the file:
ssl_protocols TLSv1 TLSv1.1 TLSv1.two; ssl_prefer_server_ciphers on; ssl_ciphers 'EECDH+AESGCM:EDH+AESGCM:AES256+EECDH:AES256+EDH'; If you desire HTTP traffic to redirect to HTTPS, you lot can add together this additional server cake at the height of the file (replace the highlighted parts with your ain information):
server { listen 80; server_name example.com; rewrite ^/(.*) https://example.com/$1 permanent; } And then salvage and quit.
At present restart Nginx to load the new configuration and enable TLS/SSL over HTTPS!
sudo service nginx restart Exam information technology out by accessing your site via HTTPS, e.g. https://case.com.
Apache
If want to use your certificate with Apache on Ubuntu 14.04, follow this section.
Brand a fill-in of your configuration file by copying it. Assuming your server is running on the default virtual host configuration file, /etc/apache2/sites-available/000-default.conf, apply these commands to to brand a copy:
cd /etc/apache2/sites-bachelor cp 000-default.conf 000-default.conf.orig And then open the file for editing:
sudo vi 000-default.conf Find the <VirtualHost *:80> entry and alter it so your web server volition listen on port 443:
<VirtualHost *:443> Then add the ServerName directive, if information technology doesn't already exist (substitute your domain name here):
ServerName example.com And then add the following lines to specify your certificate and central paths (substitute your bodily paths hither):
SSLEngine on SSLCertificateFile /domicile/sammy/example.com.crt SSLCertificateKeyFile /dwelling/sammy/example.com.key If y'all are using Apache 2.iv.8 or greater, specify the CA intermediate package by adding this line (substitute the path):
SSLCACertificateFile /habitation/sammy/intermediate.crt If you are using an older version of Apache, specify the CA intermediate bundle with this line (substitute the path):
SSLCertificateChainFile /habitation/sammy/intermediate.crt At this signal, your server is configured to heed on HTTPS only (port 443), so requests to HTTP (port 80) will not be served. To redirect HTTP requests to HTTPS, add the post-obit to the top of the file (substitute the name in both places):
<VirtualHost *:80> ServerName instance.com Redirect permanent / https://example.com/ </VirtualHost> Save and exit.
Enable the Apache SSL module by running this control:
sudo a2enmod ssl At present restart Apache to load the new configuration and enable TLS/SSL over HTTPS!
sudo service apache2 restart Test it out by accessing your site via HTTPS, e.g. https://instance.com. You will as well desire to try connecting via HTTP, eastward.g. http://example.com to ensure that the redirect is working properly!
Conclusion
Now you should have a proficient idea of how to add together a trusted SSL certificate to secure your web server. Be sure to shop around for a CA that you are happy with!
Source: https://www.digitalocean.com/community/tutorials/how-to-install-an-ssl-certificate-from-a-commercial-certificate-authority
Posted by: connellremon1937.blogspot.com


0 Response to "How To Install Ssl Certificate Digitalocean"
Post a Comment